The chip was developed as part of DARPA’s vanishing programmable resources project, and could have several practical applications in cases where extreme security measures are required. For example, top-secret data stored by the government and military might be able to benefit from a chip that could be destroyed on command. This could save some serious data leaks from occurring.
Down the line, there could be some commercial usse for chips like this. Users who are extremely security conscience may be willing to install something like this in their devices.
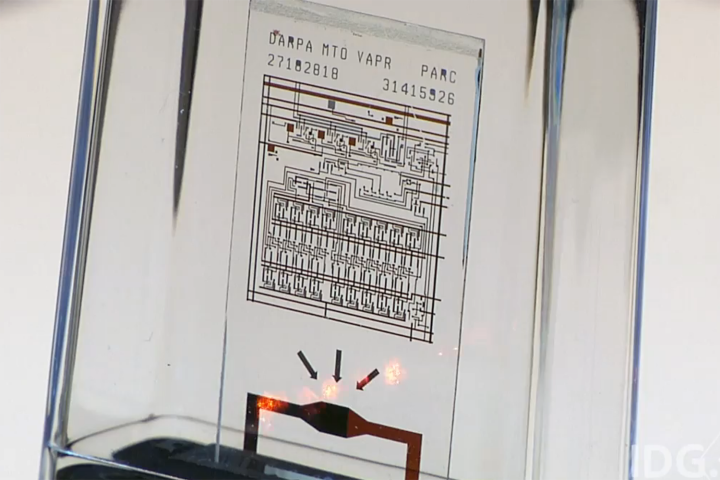
The chip is made using Corning’s Gorilla Glass — yes, the very same glass found in many smartphones on the market today. The team modified the glass to become tempered under stress. From there, a resistor at the chip’s bottom is heated with a laser, and that causes the entire chip to explode into dust. After that, the smaller glass pieces will continue to melt and explode into even smaller pieces for the next few seconds.
The entire process is outlined in the video above. The team says that a laser isn’t required to cause the chip to explode, and that anything from radio signals to a physical switch could be used to initiate the process and cause the chip to turn to dust. It sounds like a long process, but in real-time, it happens almost instantly.
“We take the glass and we ion-exchange temper it to build in stress,” explained Gregory Whiting, a senior scientist at PARC, “What you get is glass that, because it’s heavily stressed, breaks its fragments into tiny little pieces.”
As one might expect, there are no plans in place to sell these chips just yet, as they are still early in development, but it’s not too soon to think about how these might see later use.


